Top 10 Cloud Security Challenges to Overcome in 2021
Click here to read about the top 10 cloud security challenges that businesses must address in 2021.
Cloud security is defined as a set of policies, controls, procedures, and technologies applied to a cloud network to protect cloud-based systems, data, and infrastructure. A cloud security system protects cloud data, keeps customer privacy intact, and consequently maintains regulatory compliance for cloud users. This article gives a comprehensive view of the top 10 cloud security challenges that 2021 needs to address.
Table of Contents
Need for Improved Cloud Security in 2021
Cloud security, also termed cloud computing security, is a set of policies, controls, procedures, and technologies applied over a cloud network to protect cloud-based systems, data, and infrastructure. Cloud security can be configured to match various business needs, where policies can be set-up right from authenticating user access to filtering cloud traffic.
Cloud security enables businesses to configure and manage security rules from a single access point, thereby reducing the administration overheads and allowing IT teams to focus on other critical areas of the business apart from security. Although the delivery of cloud security depends on the individual cloud provider, the implementation of cloud security processes as a whole is a joint responsibility between the business owner and the cloud solution provider.
Businesses adapted to a new normal by opting for digital operations amid the pandemic. To fuel the digital-first strategy, enterprises are increasingly embracing cloud platform services to support their remote workflows. As cloud initiatives continue to accelerate in 2021, organizations must ensure that proper security and governance measures are implemented to keep their data secure and avoid financial losses.
Here are some plausible reasons to prioritize cloud security in 2021.
1. Everywhere enterprise
As we close in on 2021, it is evident that the change in work life that 2020 introduced is here to stay. Enterprises are transforming as they continue to uphold remote working practices to adhere to government guidelines. 2021 is now seen as the age of “everywhere enterprise”, with the maximum workforce working from home.
The COVID-19 pandemic has seen many companies move to the cloud as they seek more enterprise-level collaboration and productivity tools for a remote employee base. As more organizations join hands with the cloud infrastructure, we expect the upward surge to continue in 2021. Businesses have accepted the new working models — they are prepared to preserve them in the long term, or perhaps permanently. Tech giant Google has urged employees to continue remote work until at least July 2022, whereas Twitter has allowed some of its staff to work from home permanently.
With the rise in remote workforce in the age of everywhere enterprise, businesses need to upgrade their cloud security. Data is accessible from anywhere to anyone and is also vulnerable to cyberattacks.
Also Read: What Is Private Cloud Storage? Definition, Types, Examples, and Best Practices
2. Fading traditional remote access mechanisms
In the older cloud model, companies used a full VPN to tunnel all traffic via the enterprise network. Such architecture introduced latency issues, especially when accessing applications in the cloud, because it meant routing all traffic back through the enterprise data center. Come 2021, companies should stop routing cloud sessions via the enterprise network.
Instead, enterprises should allow remote workers to access them directly. This calls for two possibilities, either sanitize the traffic on the device itself or filter the traffic in the cloud. To opt for one of these possibilities, companies need to upgrade their traditional cloud security design, where the cloud network employs more computing resources to support secure traffic flow over the cloud.
3. Multi-cloud adoption continues to accelerate
According to a recent survey by Gartner, 81% of organizations work with two or more cloud providers already. This trend toward multi-cloud adoption will only accelerate in 2021. Now, as organizations and managed service providers (MSPs) accelerate cloud initiatives to support remote work and learning amid the COVID-19 pandemic, they are expected to gain a deeper understanding of the pros and cons of each public cloud provider.
After understanding the different types of applications that run better in some cloud environments, the need for adopting more than one cloud provider will become clearer. As the multi-cloud adoption trend goes into 2021, cloud security will play a more crucial role for any organization to safeguard its data from cyber threats.
Also Read: What Is Virtual Private Cloud (VPC)? Definition, Key Components, Best Practices, and Providers
4. Securing and governing multi-cloud environments
With digital transformation at its peak, the self-service nature of cloud infrastructure is susceptible to more user mistakes. One such mistake could be granting access to users or machines that should never have been granted. To make matters worse, cloud’s lack of visibility makes these mistakes challenging to identify or locate and remediate.
Gartner predicts that through 2025, 99% of cloud security failures will be the customer’s fault, and 90% of organizations that fail to control public cloud use will inappropriately share sensitive data. This will make identity and access management (IAM) an important factor for individual and machine users to handle cloud security systems in 2021.
Thus, multi-cloud environments will continue to increase in 2021. As a result, organizations will increasingly need to implement cloud ownership guidelines and governance policies to visualize who has access to specific resources in the cloud.
5. Businesses continue to look to MSPs for guidance
According to a recent report by Gartner, security spending is expected to grow 2.4% to reach $123.8 billion in 2020. These figures are down from the 8.7% growth previously projected by Gartner in its December 2019 forecast.
Although the spending goes down, the expectations of security continue to remain high. Therefore, organizations will largely depend on MSPs for guidance on managing, governing, and securing their IT operations in a cost-effective manner. This will balance the increasing budgetary pressures while supporting a secure and productive remote workforce.
Also Read: Network Security Engineer: Job Role and Key Skills for 2021
6. More global companies than ever before
Cybersecurity has seen a talent gap for years, making it difficult for organizations to recruit and retain the security professionals they need. However, as companies shifted to remote work in 2020, it has become more evident that people can perform their jobs from almost anywhere.
This gives companies the license to cash-in on a geographical pool of candidates for new hires in various business departments, including security. Such globalization demands security to evolve to a more democratized approach, ensuring that security is delivered at the edge and on the various endpoints used by the global workforce. This will draw curtains on the centralized security strategy by the time we head into 2021.
Although the future seems uncertain, there are several aspects that an enterprise can control in 2021. One of them is controlling the cloud environment to ensure that data stays secure, thereby avoiding data breaches which cost companies about $3.86 million per breach (on average). As multi-cloud adoption continues to accelerate, organizations must have clear visibility of their cloud environment, ensure cloud governance policies are in place and strengthen the MSP front to aid in cloud management.
Also Read: Top 10 Facial Recognition Software in 2021
Top 10 Cloud Security Challenges to Overcome in 2021
According to Gartner, the end-user spending (globally) on public cloud services is forecast to grow 18.4% in 2021 to a total of $304.9 billion — which is substantially up from $257.5 billion in 2020. As the demand for cloud continues to soar high amidst the pandemic, organizations must understand what challenges cloud computing brings to the table. Cloud Security Alliance presented a report that focused on cloud security concerns. As we head into 2021, here are the top 10 cloud security challenges that organizations need to address.
1. Abuse of cloud services
Abusive use of cloud services refers to attackers leveraging the cloud computing resources to target users, organizations, and other cloud providers. Examples of such abusive usage include launching DDoS attacks, phishing, email spams, and more. Further, malicious attackers can also host malware on cloud services and make them look more legitimate because the concerned malware uses the CSP’s domain.
Here, the cloud-hosted malware can additionally use cloud-sharing tools as an attack vector to propagate itself further. In 2021, companies should have more control over the entire cloud framework while keeping an eye on cloud services being attacked or abused by cybercriminals.
2. Cloud account hijacking
In cloud account hijacking, an individual or organization’s cloud account is stolen or hijacked by an attacker, and the stolen account information is used to conduct malicious or unauthorized activity. Cybercriminals tend to abuse accounts that seem to have highly privileged or sensitive data.
In cloud environments, cloud service accounts or subscriptions are highly susceptible to hijacking. These accounts can be compromised if attackers employ certain forms of phishing attacks, exploit the cloud-based systems, or steal cloud or user credentials.
Also Read: Top 10 Private Cloud Hosting Solution Providers in 2021
3. Cloud misconfiguration
Cloud misconfiguration refers to a situation where an unencrypted data store is left exposed to the public. Anyone can access the store without any form of authentication via the internet. This exposes cloud data to all global users of the same cloud platform, leaving user credentials and encryption keys in open repositories. Security misconfiguration is one of the common cloud challenges today.
In 2017, a misconfigured AWS Simple Storage Service (S3) bucket exposed the private data of about 123 million American households. The data set belonged to credit bureau Experian, which sold the data to an online marketing and data analytics company called Alteryx. It was Alteryx that exposed the file. Such misconfiguration instances can be disastrous for any cloud-operated organization.
4. Cloud usage visibility
When an organization does not exercise its ability to analyze whether a cloud service used within the organization is safe or malicious, it may lead to potential security breaches in the cloud network. The concept of cloud usage visibility can be segregated into two specific challenges.

Cloud Usage Visibility
a) Unsanctioned app use
This occurs when employees use cloud applications and resources without the specific permission and support of corporate IT and security. This can result in a self-support model called shadow IT. According to Gartner, about 1/3rd of all successful security attacks on companies come through shadow IT systems and resources.
b) Sanctioned app misuse
Organizations are often unable to analyze how their approved applications are being leveraged by insiders who use a sanctioned app. This use occurs without the explicit permission of the company or by external threat actors who target the service using domain name system (DNS) attacks, credential theft, and more.
Also Read: Private vs. Public Cloud: 10 Key Comparisons
5. Data breaches
A data breach is an intentional or unintentional release of secure or confidential information to an untrusted party. According to a recent research study conducted by IDC, nearly 80% of companies experienced a cloud data breach in the past 18 months. Data breaches can have dreadful consequences for any organization. Some of these include:
a) Reputation and trust of customers are lost.
b) Intellectual property (IP) is under threat as competitors can gain an advantage over your IP data — which can further impact future product releases.
c) Financial losses are incurred due to incident response and forensics.
d) Brand value can go to an all-time low due to the reasons listed above.
6. Insecure interfaces and APIs
Cloud customers interact with cloud services via a set of software user interfaces (UIs) and APIs. Thus, the availability of general cloud services relies on the security of these UIs and APIs. These UIs must be designed to protect against accidental and malicious attempts to strengthen the cloud security policy right from authentication and access control to encryption and activity monitoring.
Poorly designed APIs such as broken or hacked APIs can cause major data breaches. Therefore, organizations need to understand the security requirements around designing and presenting these interfaces to their customers over the internet.
Also Read: Top 10 Customer Identity Management Solutions in 2021
7. Insider threats
Insiders can be more dangerous to an organization than outside attackers for the simple reason — they are already inside. A Netwrix 2018 Cloud Security Report indicates that 58% of companies attribute security breaches to insiders. Insider negligence is the root cause of most security incidents hurting corporate companies today.
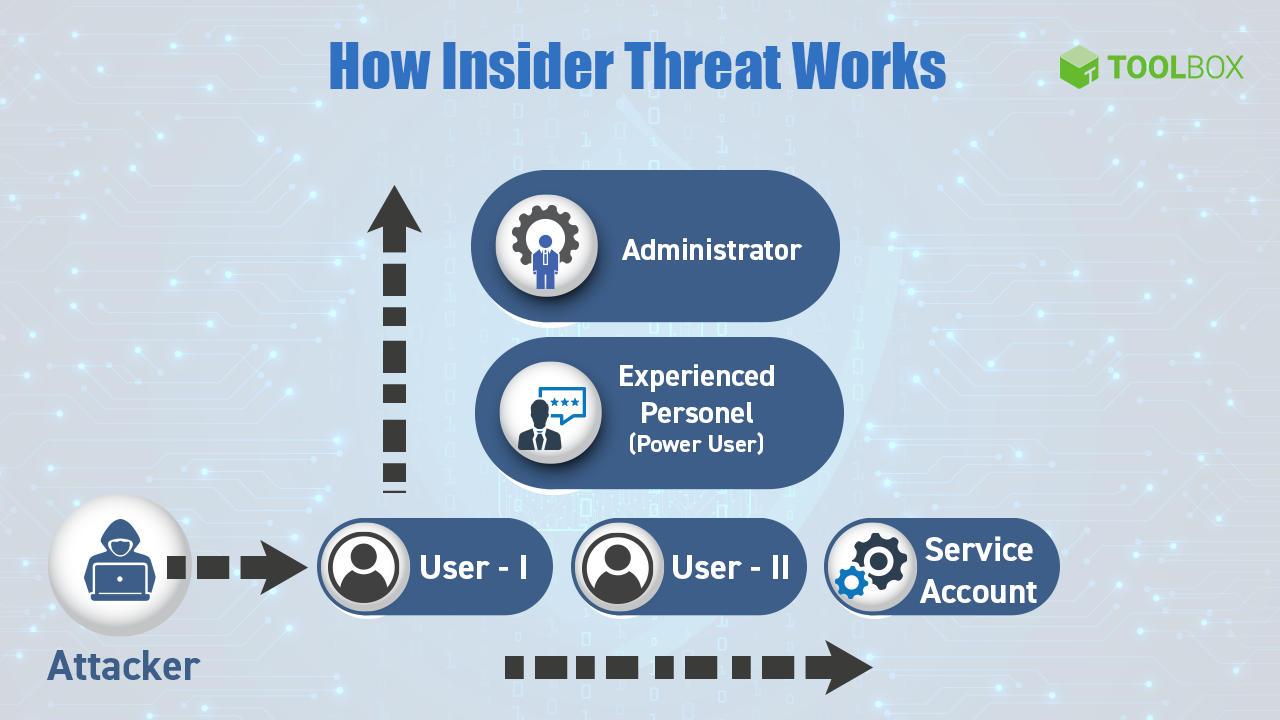
How Insider Threats Work
According to the Ponemon Institute’s 2018 Cost of Insider Threats study, negligent insiders were the root of most incidents (64%), followed by criminal and malicious insiders (23%) and employee and contractor negligence (13%). Some common insider-based scenarios cited in the study include misconfigured cloud servers, employees storing sensitive company data on their own insecure personal devices and systems, and employees or other insiders falling prey to phishing emails.
8. Lack of identity, credential, access, and key management
Identity and access management (IAM) implies that the same identity is used and managed for all applications, and security is kept intact across applications. It is used to authenticate users, devices, or services and grant or deny access to data and other system resources.
Cloud computing has brought about significant changes to traditional internal system management practices of IAM. In both public and private cloud frameworks, cloud service providers and cloud consumers must manage IAM without compromising security. Hence, in 2021 as companies adopt a multi-cloud environment, managing IAM efficiently will play a crucial role.
Also Read: Cloud vs. On-premise Comparison: Key Differences and Similarities
9. Robust cloud security architecture
Cloud security architecture is a strategy designed to secure and view an organization’s data and collaborative applications in the cloud. This is done through the lens of a cloud provider. The pandemic has forced organizations globally to migrate portions of their IT infrastructure to public clouds. Such transition demands an appropriate implementation of cloud security architecture to withstand cyberattacks.
Lack of proper cloud security architecture and strategy has exposed the data to different threats. Organizations assume that applications and associated data can be migrated to cloud via a “lift-and-shift migration approach”, wherein the existing IT stack and security controls are ported to the cloud environment. Thus, there lies a gap in understanding the shared security responsibility model, which organizations must prioritize for efficient cloud security management.
10. Weak control plane
Creating sufficient data storage and applying appropriate protection program can pose a serious challenge while moving the organizational framework from the data center to cloud. As the multi-cloud trends continue to rise, organizations must develop new processes for data duplication, migration, and storage. A strong control plane can provide an effective solution to these problems, as it enables the security and integrity that would complement the data plane that provides stability in runtime.
A weak control plane is linked to the in-charge personnel, either a DevOps engineer or a system architect. The person in charge is not in full control of the data infrastructure’s logic, security, and verification. In such a scenario, stakeholders do not have the knowledge of the cloud security configuration, how data flows and where architectural blind spots and weak points exist. Such limitations could eventually result in data corruption, unavailability, or leakage.
In conclusion
As cloud adoption grows, organizations’ cloud strategy must go hand-in-hand with a security strategy. Given that remote working or work from anywhere is here to stay, businesses will continue to shift to cloud infrastructure. Thus, it is now more vital for businesses to have a strong, reliable, and robust cloud security strategy in place to host a safe and secure cloud infrastructure irrespective of the ongoing cyber threats. Having a strategy in place can also help companies prevent overspending or misspending on cloud security controls.
What other cloud security challenges would 2021 have to address? Comment below or let us know on LinkedIn, Twitter, or Facebook. We’d love to hear from you!






